You probably heard about the huge hacker assault on Twitter, earlier this week. The accounts belonging to Barrack Obama, Britney Spears, Fox News and many others were broken into, and then defaced in appreciably juvenile ways. For example, Bill O'Reilly "is gay" according to his Tweeted messages he sent out, on Monday.
Wired magazine got in contact with the hacker behind the Twitter escapades. At first, it was one person who gained access to the administration accounts of the system. From there, the hacker offered free accounts to anyone who wanted them, on a forum called Digital Gangster.
As it turns out, hacking into Twitter was much easier than many probably suspected. In fact, the hacker -- whose goes by identity GMZ -- used one of the oldest tricks in the book: a brute-force dictionary attack. He found out that Twitter did not report or lock out any I.P addresses that had any number of failed password attempts, so he wrote his own little program to feed words from a dictionary, into the password field for an administration user named Crystal, one at a time, in quick succession.
The password turned out to be 'happiness.' The people who pay Crystal's salary were probably not all that happy to find out she used such a weak password.
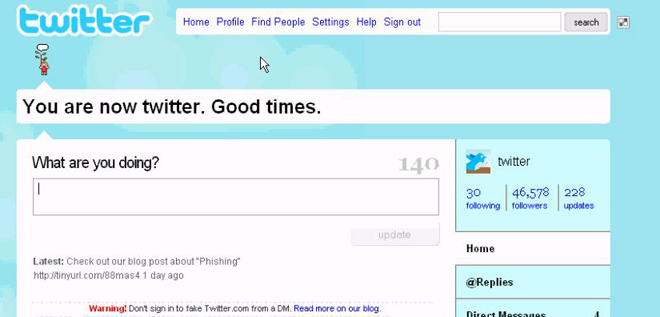
Being a cool hacker dude that he is, GMZ posted a video showing everyone that he did indeed sneak into Twitter's innards:
GMZ has also been responsible for gaining access to Miley Cyrus's YouTube account, the SayNow account of Selena Gomez, and other various celebrity accounts over various websites. He is 18 and is pursuing game development and has so far evaded prosecution for his horrible and heinous crimes.
For further information, follow the link below to Wired's Danger Room.
Damn news people. They are behind water fluoridation.
i mean....he practicly did this by trial and error
"I thought this was America"
Brute force, especially dictionary attacks are very simple to do but not the most efficient due to the time constraints it takes. But they *do* work and are still popular methods. It's not like it's out dated and is a shock that omg it's 2009 and people are still doing this?!
As for simple passwords not *everyone* is going to be the savviest when it comes to technology, no matter what year it is. Her employers can't be upset with her as it is their own liability to ensure that all employees are knowledgeable on retaining secure passwords, not to write them down, etc, etc. Also, it is a systems admin error by not logging / tracking security issues such as this.
Allowing your system to be open to brute force attacks, which pretty much any person with a basic programming knowledge can exploit, is not very 2009, in regards to security, in my opinion.
I'm surprised that such a major website would be open to a brute force attack. I thought a most basic-level security precaution was to limit the amount of login tries someone could have in a short amount of time.